Access Management and Abuse Prevention for Generative AI (Echo AI)
JWT auth, IP verification, and per-user credit management in one n8n workflow — the security backbone that keeps the Echo AI platform abuse-free and scalable.
Discuss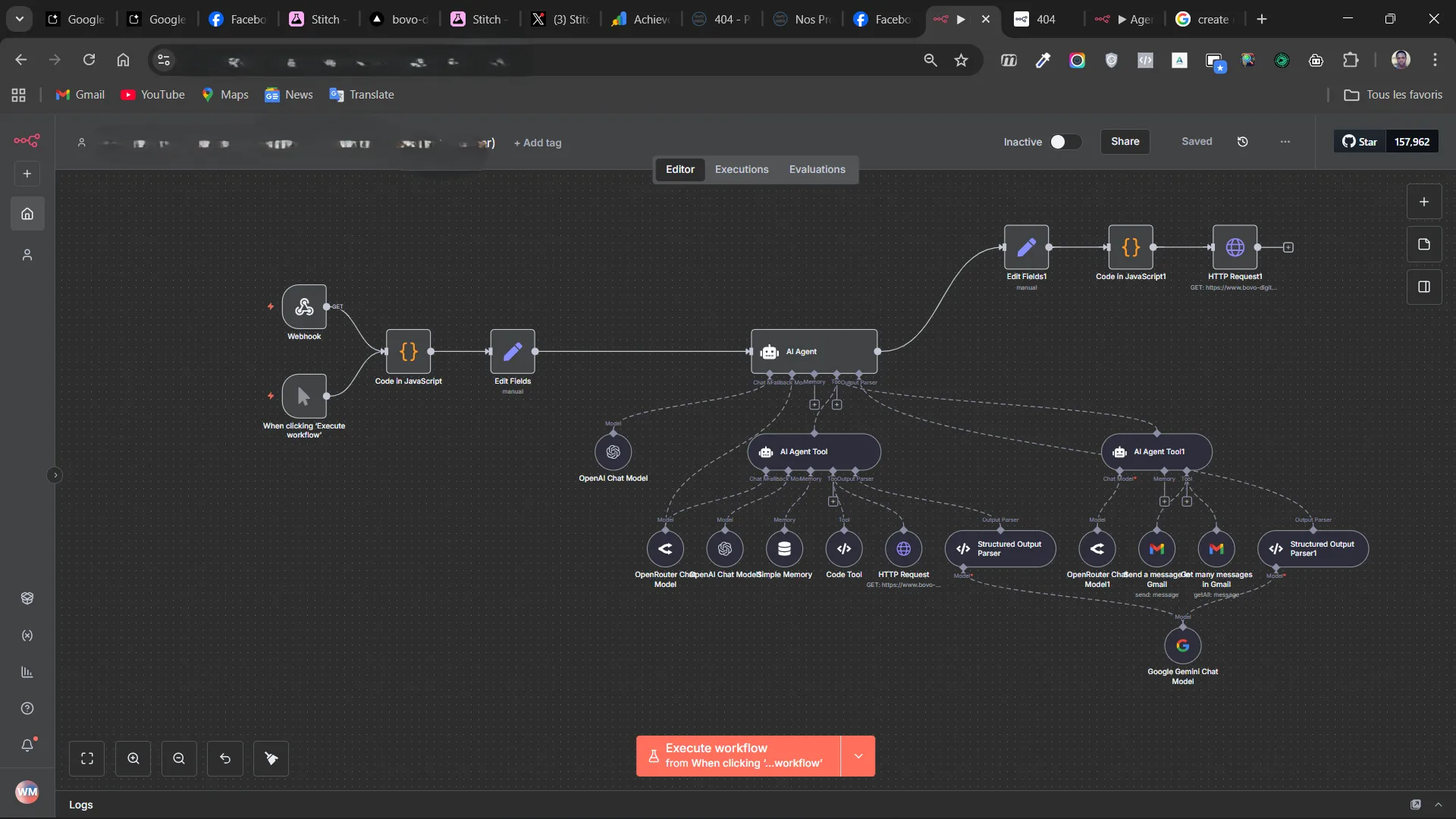
About this project
Automation Workflow for Security and Access Management (Echo AI)
Project Context This project is part of a complex backend architecture designed to power "Echo AI," an innovative application. Echo AI allows users to transform a simple product image and an inspiration image into a professional creative brief for advertising, merging styles and products to generate impactful visuals. My role was to create an essential pillar for the sustainability and integrity of this service.
Challenge and Objective The main objective was to implement a sophisticated access control system to prevent abusive and unauthorized use of the Echo AI application, while efficiently managing the resources (credits) allocated to users. Without such a system, the infrastructure could be overwhelmed by malicious or excessive requests, leading to unforeseen costs and degradation of the legitimate user experience.
Implemented Solution I designed and deployed a powerful automation workflow using n8n. This workflow acts as an intelligent guardian, integrating several security and management mechanisms:
Credit Management: Precise tracking of credit usage per user, ensuring that each interaction complies with defined quotas. IP Address Verification: Implementation of IP-based controls to identify and block suspicious or excessive traffic sources. JWT Authentication: Use of JSON Web Tokens (JWT) to secure access to functionalities, guaranteeing that only authenticated and authorized requests are processed. Robust Data Storage: Integration with Google Sheets for dynamic and easily accessible management of user data and security configurations. Webhooks and Integrations: Leveraging webhooks for fluid communication between different parts of the system, allowing real-time responsiveness to requests.
Impact and Results This system effectively secured access to Echo AI, significantly reducing the risks of abuse and optimizing resource usage. It ensures a fair and reliable user experience while protecting the operational integrity of the application. The modularity of the n8n workflow also offers great flexibility for future evolutions and adjustments of access policies.
Ready to automate your business? → Discover our AI Automation service
